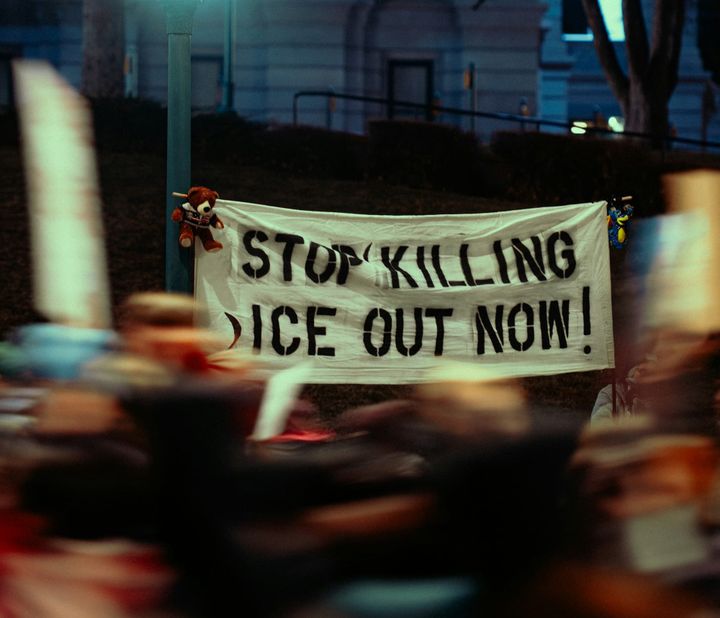
"Why hack the DHS? I can think of a couple Pretti Good reasons!"

Is everyone in your Signal groups named something like "E" or "🥑"? Nicknames can help!

Jeffrey Epstein Bought Books About Pedophilia, Woody Allen, and Trump

How to easily dig through the Epstein files yourself


