
The Signal Clone the Trump Admin Uses Was Hacked
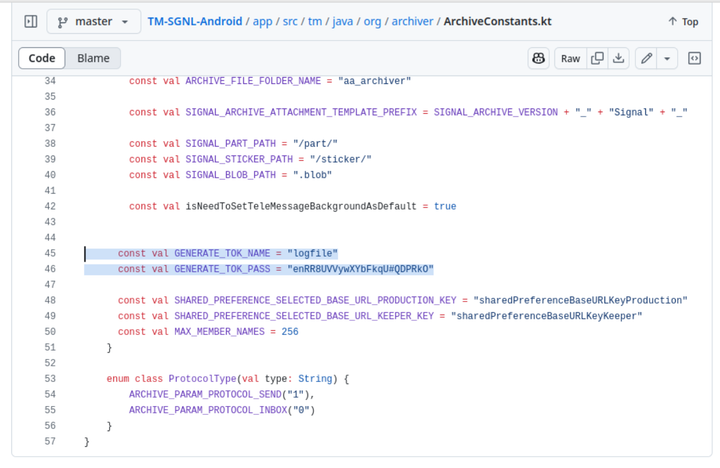
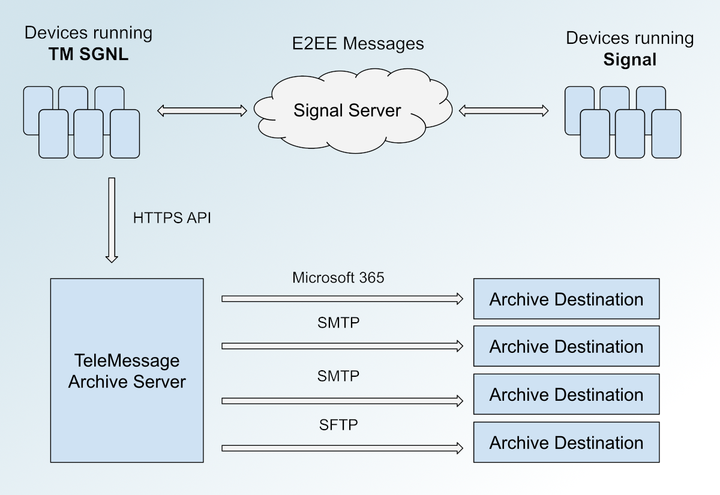
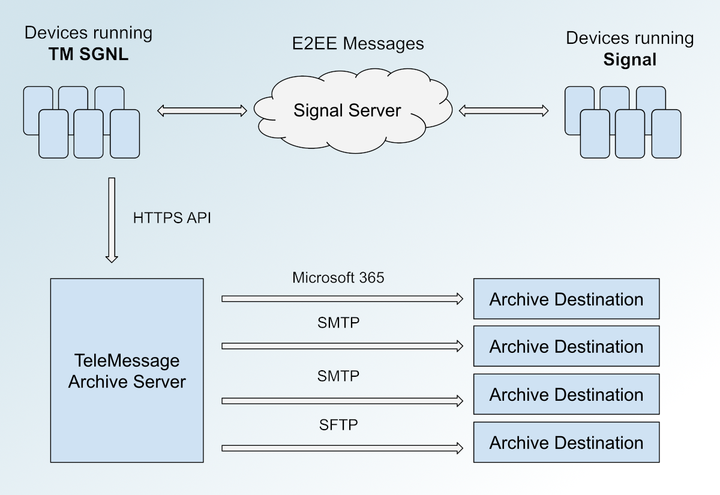
Here's the source code for the unofficial Signal app used by Trump officials
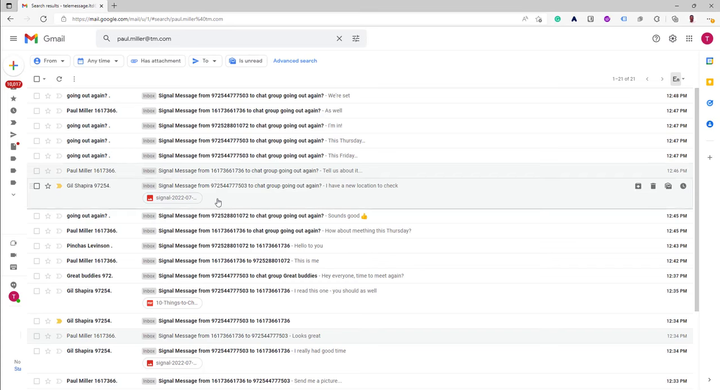
TM SGNL, the obscure unofficial Signal app Mike Waltz uses to text with Trump officials

Hunting street-level cell phone surveillance with Rayhunter


