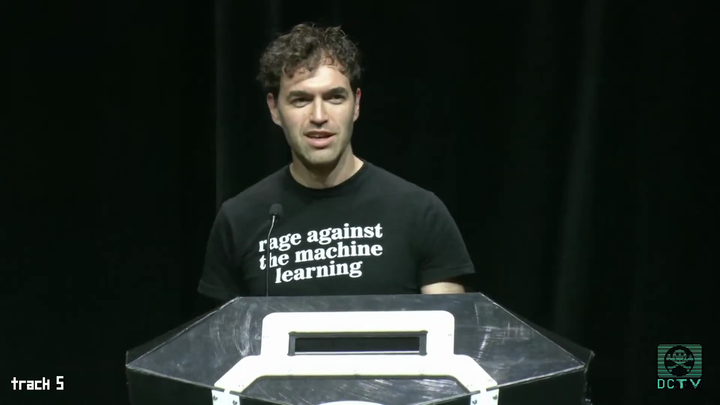
In war-torn Portland? Watch me speak at BSidesPDX!
ICEBlock handled my vulnerability report in the worst possible way
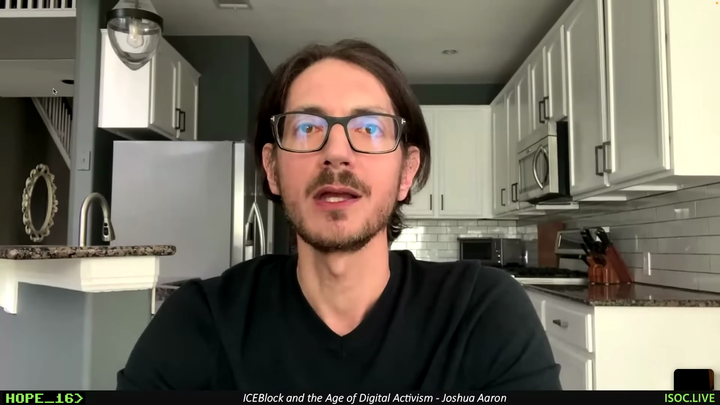
Unfortunately, the ICEBlock app is activism theater
"We are currently clean on OPSEC": The Signalgate Saga